6 Advantages and Benefits of Druva's Anomaly Detection Technology
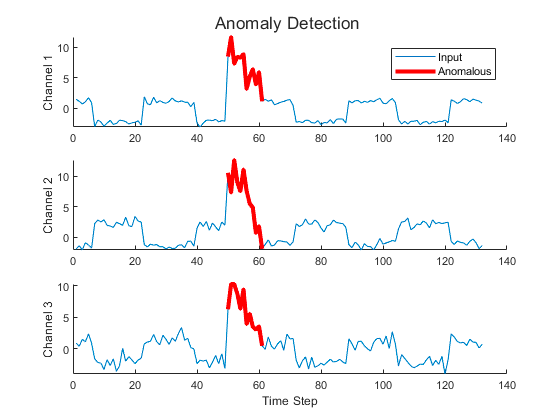
1. Enhanced Threat Detection
Druva's anomaly detection technology goes beyond traditional anomaly detection by combining machine learning algorithms and behavioral analytics to detect subtle patterns indicative of advanced threats. By continuously monitoring data activity across VMs, it can identify sophisticated attack vectors, including lateral movement, command-and-control communication, and data exfiltration attempts, empowering organizations to detect threats that may evade conventional security.
2. Risk Mitigation with Advanced Contextual Analysis
Anomaly detection not only identifies unusual data activity but also provides advanced contextual analysis. By correlating data access patterns with known threat intelligence and user behavior profiling, Druva's anomaly detection can differentiate between legitimate activities and malicious actions, reducing false positives and providing security teams with actionable insights to prioritize and respond to real threats effectively.
3. Real-time Threat Intelligence and Automated Response
Druva's anomaly detection technology operates in real time, continuously analyzing data activity and providing security teams with real-time threat intelligence. By leveraging this intelligence, organizations can automate incident response actions, such as blocking suspicious IP addresses, isolating compromised systems, or quarantining infected files. This automated response capability accelerates incident response times, reduces manual intervention, and minimizes the potential impact of security incidents.
4. Holistic Visibility and Forensic Investigations
Anomaly detection enhances visibility into data activity across VMs, enabling comprehensive monitoring and forensic investigations. Detailed logs and reports provide security teams with the necessary visibility to trace the root cause of an incident, identify affected systems or users, and determine the extent of the compromise. This level of visibility enables organizations to conduct thorough investigations, strengthen security controls, and learn from past incidents to prevent future occurrences.
5. Integration with Threat Intelligence Platforms
Druva's anomaly detection seamlessly integrates with third-party threat intelligence platforms, allowing organizations to leverage additional threat intelligence sources and enrich the detection capabilities of anomaly detection. By integrating with external threat intelligence feeds, organizations can enhance their understanding of the threat landscape, identify emerging threats, and stay ahead of potential risks. Druva offers prepackaged integrations with many SIEM and SOAR tools, such as FireEye and Splunk, to further monitor compliance and configure smarter alerts as well as forensics.
6. Compliance and Data Governance
Anomaly detection plays a vital role in helping organizations meet regulatory compliance requirements and maintain robust data governance practices. By monitoring data access patterns and detecting anomalous behavior, Druva's anomaly detection enables organizations to identify potential data breaches or unauthorized data access, ensuring compliance with data protection regulations and safeguarding sensitive information.
Next Steps
In an era of rapidly evolving cyber threats, organizations must adopt advanced technologies to fortify their security posture and protect their valuable data. By partnering with Druva and leveraging anomaly detection, organizations can enhance their security posture, protect against emerging threats, and confidently navigate the ever-changing landscape of cybersecurity.
Learn more about how Druva enhances organizations’ security posture and observability and take a product tour here to see Druva in action. Get the technical details for implementing and leveraging anomaly detection in your Druva instance on the Druva documentation portal.