The Covid-19 pandemic started a transformation in the way people work. The shift towards remote and hybrid work has necessitated changes in data management practices. First, organizations need data management across their user data including Endpoints, Microsoft 365, and other SaaS applications because user, security, and regulatory needs apply to the data, regardless of where it is stored. Second, organizations need a documented cyber recovery plan to be able to recover from an attack because user data is both an attack vector and a target for cybercriminals.
Introduction
Every shift (new technology adoption, operational or work culture) is preceded by an inflection point and the Covid-19 pandemic was the inflection point that accelerated the adoption of remote work practices, compelling enterprises to adapt their operations. Thus, the storage and security of data have become of paramount concern. This paper explores the challenges faced by enterprises in a hybrid work environment, focusing on platforms like Endpoints, M365, and other SaaS applications. It delves into the implications for data security threat surfaces and outlines strategies to protect data while adhering to governance and legal requirements. Furthermore, it addresses the challenges of data restoration at scale and offers insights into planning for effective data recovery.
Data Storage in the Hybrid Work Environment
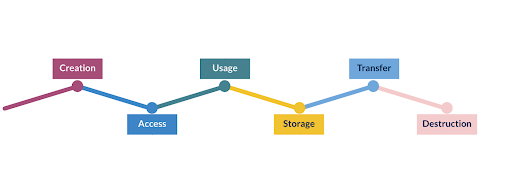
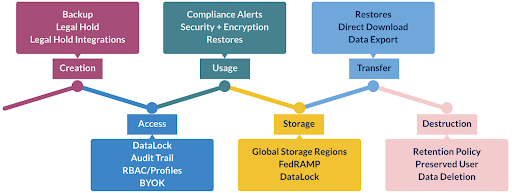
In the hybrid work environment, enterprises rely on a combination of their laptops and SaaS applications to execute their day-to-day activity, so their data is distributed across multiple repositories and geographic locations. Microsoft 365 has emerged as a popular choice due to its collaboration features (read ExchangeOnline) and integration with other productivity tools. SharePoint Online and OneDrive for Business provide a centralized repository for documents, while Teams serves as a hub for communication and file sharing. These platforms enable enterprises to access and collaborate on data regardless of their physical location. Regardless of where data is created, stored, and accessed (laptop or M365), it goes through the data lifecycle - from creation to usage through destruction. Data must be protected and secured throughout the lifecycle.