Watch the video below as I break down my experience deploying Druva’s direct-to-cloud solution in an Oracle 21c database.
Tech/Engineering, Product
A First Look at Druva’s Container Database Support for Oracle

Oracle’s multi-tenant feature offers its end-user community a containerized database that is very flexible and easy to use. The architecture comprises the creation of a CDB or container database as well as its attendant PDBs or pluggable databases. The CDB is typically referred to as the root database which is a collection of schemas, schema objects, or non-schema objects to which all PDBs belong. In recent history, I deployed Oracle 21c to my lab environment. I was quite surprised to see that the default settings in the DBCA, or database configuration assistant, prompt the end user through the deployment of a CDB right out of the box enabling you to choose defaults and avoid the advanced configuration menu.
The 21c had a number of anomalies I found surprising. First, the $ORACLE_HOME/dbs directory was empty and a $ORACLE_BASE/dbs directory had been created; it was there that the password file, spfile, pfile, .dat, and instance lock files were located. This was a bit of a change and a shock! However, it tends to indicate to the end-user community a new direction for Oracle’s RDBMS technology. This appears to be the next wave of the future where third-party vendors steer the end-user community toward using this container database technology!
As Senior Solutions Architect for Databases here at Druva, I am extremely proud of our products, so I deployed our DTC, or Direct To Cloud, Oracle data protection to the newly created 21c database. Our software agent deployed to the Linux Redhat server easily discovered the database as well as its CDB architecture. In recent history, Druva also deployed a very advanced version of Oracle Real Application Cluster data protection which protects the multi-tenant architecture perfectly, and which I will explain further in a future blog. I wanted to see how this software would work with 21c, which is quite new!
The deployment of 21c is as a typical DBA expects, a download from OTN before starting the Oracle universal installer for the software before leading into the prompts for the DBCA, or database configuration assistant, to complete the installation by creating a database. Once having done so, it is of course time to explore! An investigation then begins to reveal the new parameters, the new twists and turns that the Oracle developers have chosen to lead you on in the new release, as well as the actual technology and what features and functionalities the particular release offers the community.
Below is a screenshot of the 21c database in our Druva DTC console displaying the corresponding version of the database.
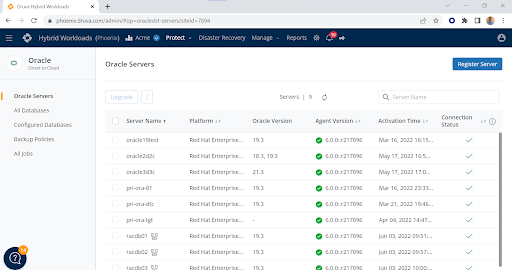
The 21c database resides on the oracle3d3c server in the Servers page of the Oracle data protection for DTC. The agent has a checkmark for connection and reports the version of the agent and the database, as well as its date of activation in the console.
When navigating to the Configured Databases page, one will see a more granular display of the configuration revealing the protection of the container database and its attendant configuration. First, click on Configured Databases then underneath the name of the database, in this case dev21c.
Below is a screenshot of the Configured Databases page with the 21c database:
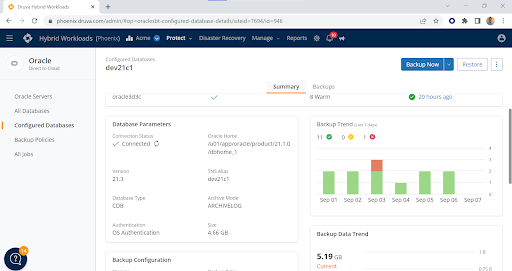
The Database Type shows as CDB, or container database, and displays the archivelog mode as well as authentication and relevant data protection elements. The DTC product affords the DBA the ability to authenticate through an Oracle wallet, OS authentication, or database authentication. The Druva agent is intelligent and capable of backing up the wallet as well as the server-side parameter file and the control file, along with all other attendant files like datafiles and/or archivelog files. This type of data protection is unique in that other data protection vendors have yet to focus on protecting these critical data elements in the multi-tenant configuration. Druva offers data protection for any multi-tenant configuration running on Real Application Clusters, or with these new container databases in a stand-alone environment!
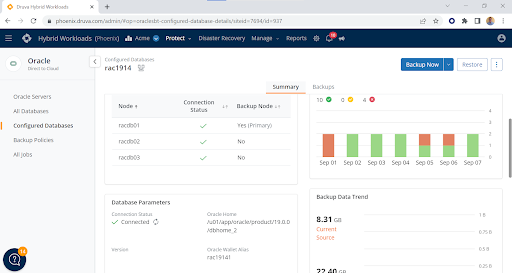
I am also including in this blog post a screenshot of our RAC data protection that displays the wallet authentication and wallet backup capabilities. It is this attention to Oracle detail and granularity that sets Druva’s Oracle data protection aside from the competition! As Oracle continues to develop its RDBMS technology at light speed, Druva is, of course, keeping abreast of these changes and continuing to add feature-rich functionality to protect your Oracle relational databases to the greatest extent possible!
The RAC configuration below has three nodes using ASM, automatic storage management, and an Oracle wallet for authentication. The below RAC configuration is using Oracle 19.14, one of the latest versions of 19c running in a virtualized environment. Note that the agent is installed on all three nodes to provide the ultimate data protection from any instance in the cluster! You may even set a primary node affinity for where the backup will run! In this case, it is node one.
Visit Druva’s Oracle page to further explore how your IT team can improve Oracle data protection with cloud backup-as-a-service, and download the DBA’s guide to Oracle data protection for a comprehensive look at best practices.
