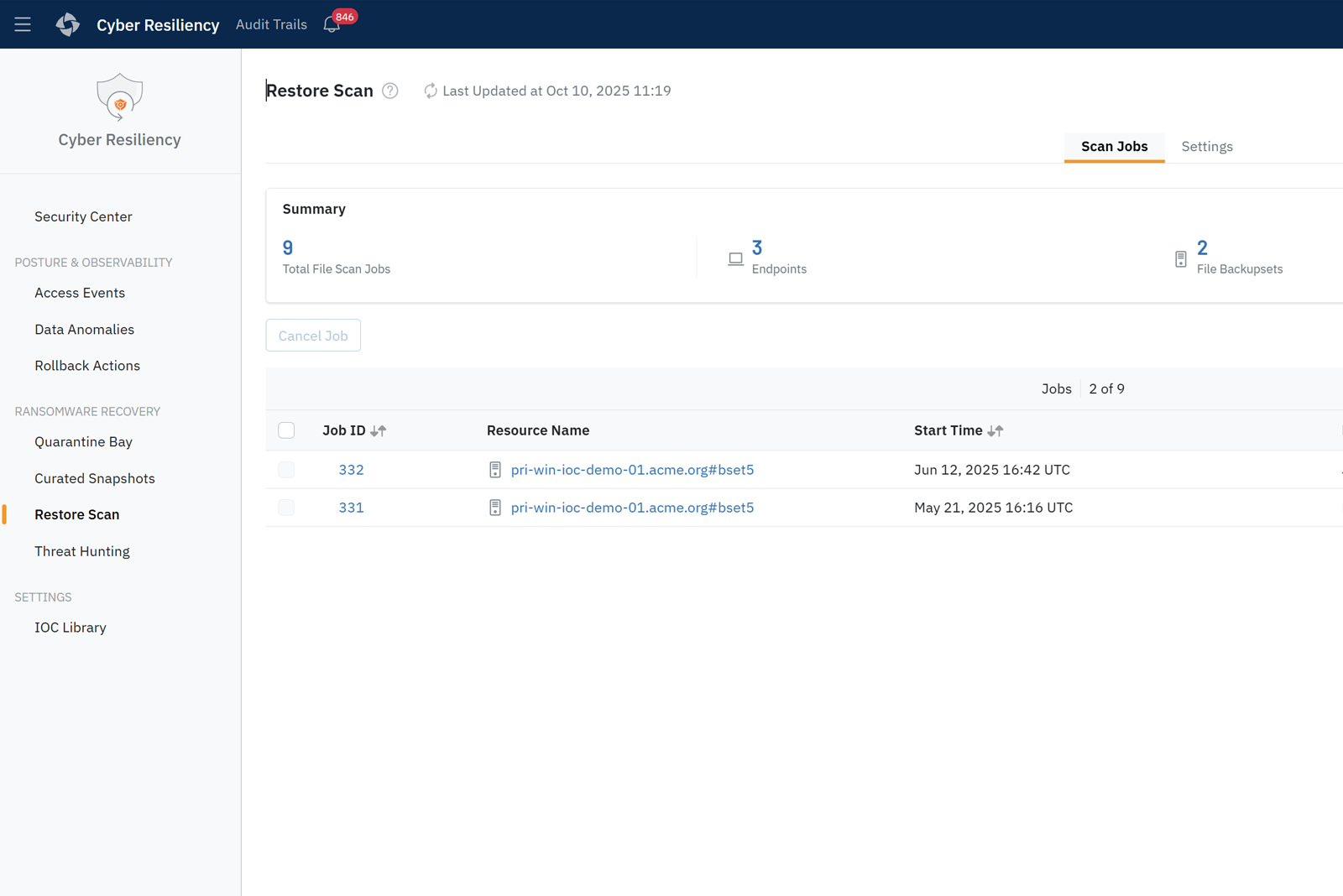
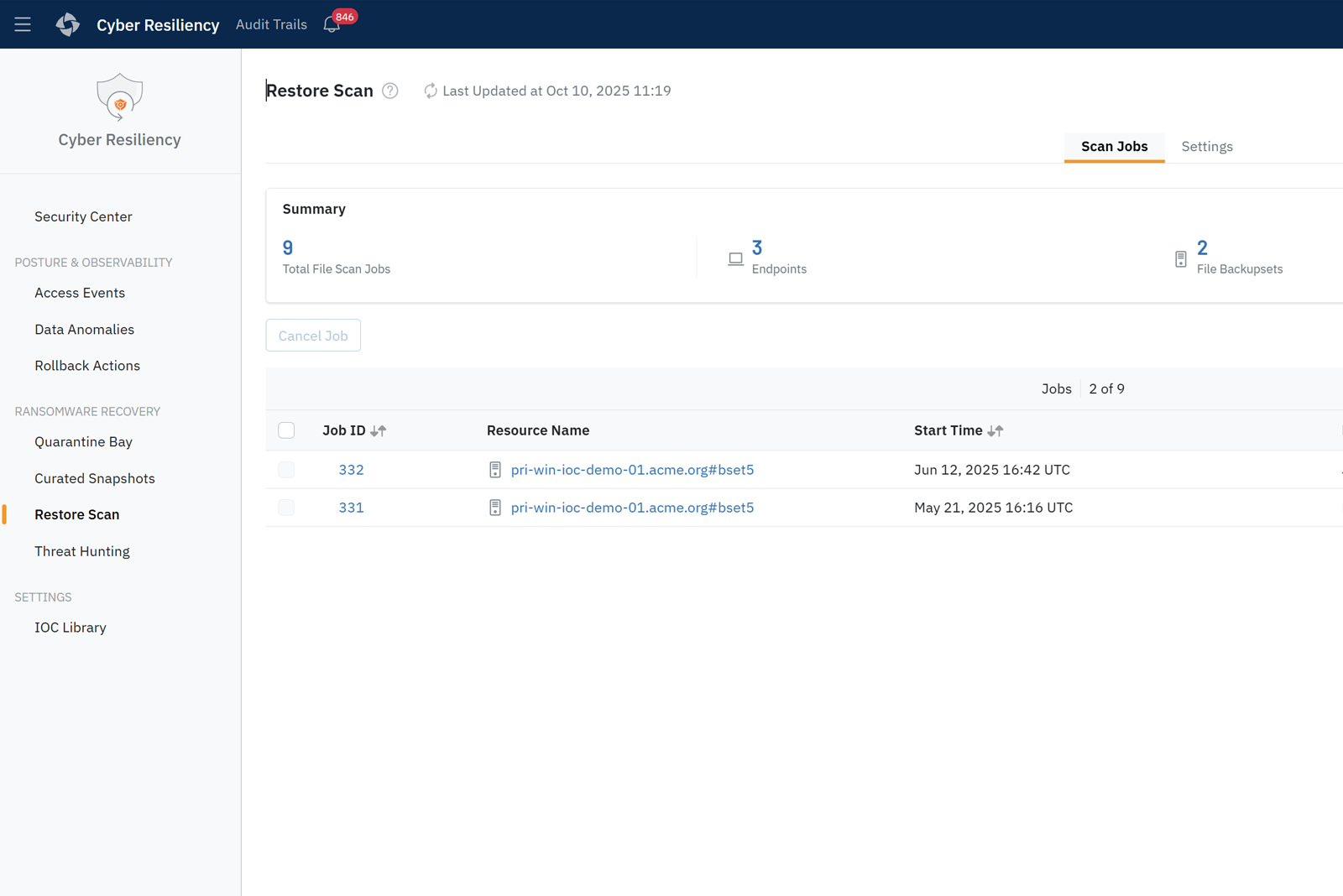
Scan data for malware during the restore process to ensure only clean files are recovered. Druva uses an antivirus engine to block malicious hashes/IOCs.
Ransomware is targeting backups
Ransomware attacks are increasingly targeting backups, but a fast and easy recovery will minimize downtime and get you back to business quickly.
Block attacks against your backups
Zero-trust security and 24x7 managed security operations enable operational security. Immutable, air-gapped backups ensure you have clean data to recover.
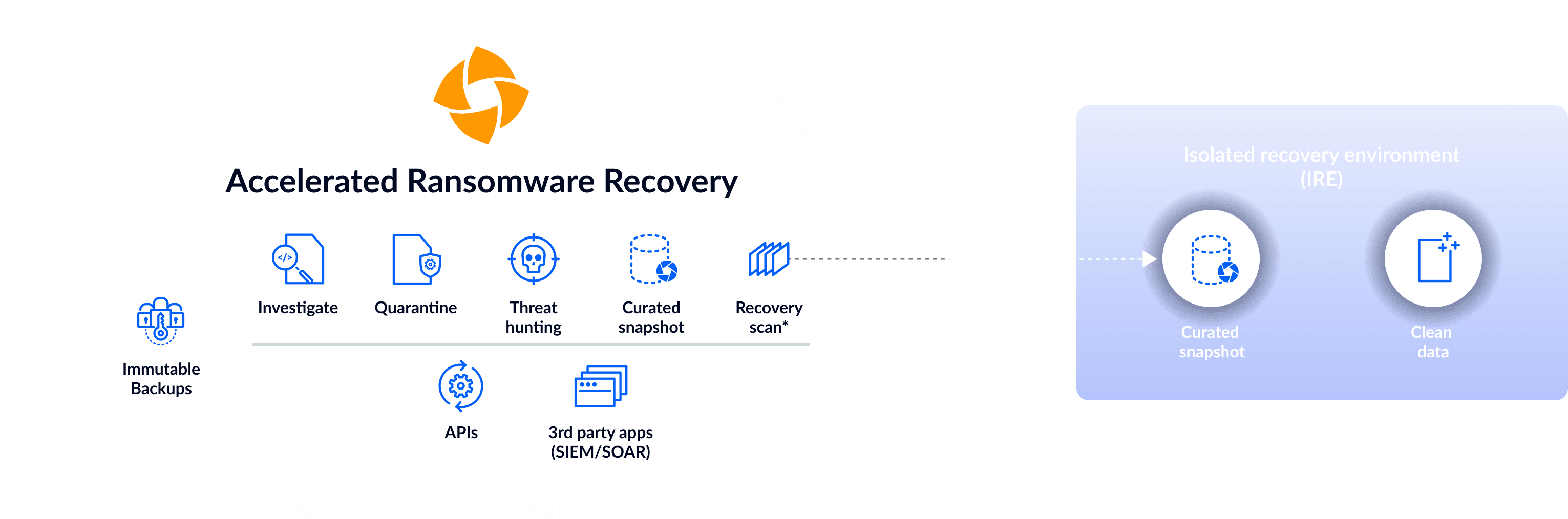
Accelerate ransomware recovery
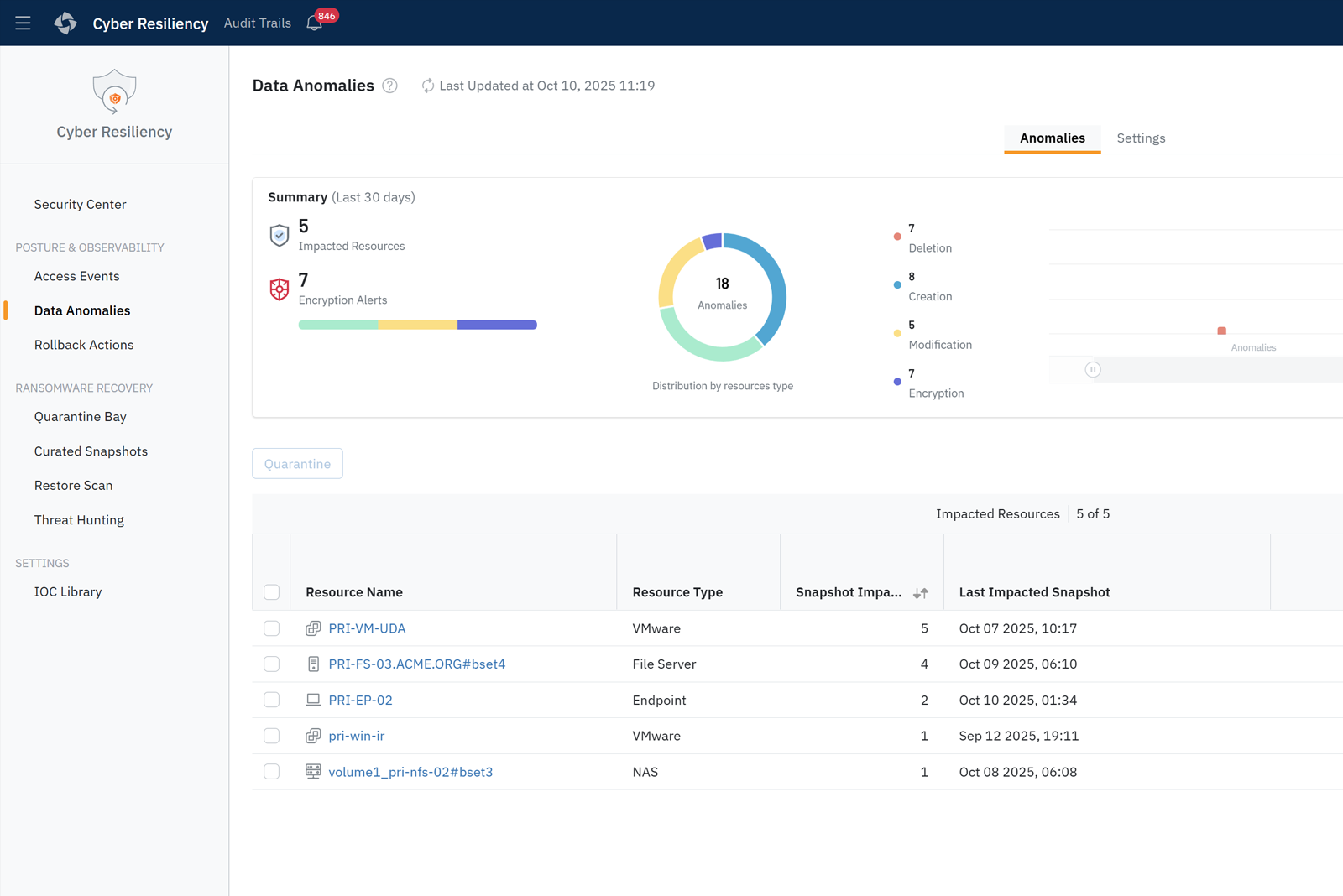
Quickly identify unusual activity and prevent contamination spread within minutes of ransomware detection. Scan snapshots before recovery to eliminate reinfection.
Bridge the gap between backup and security systems
Help IT and security teams work together with built-in integrations with SIEM and SOAR tools to automate response and recovery.
Managed data detection and response (DDR)
Druva experts monitor your backups 24/7, examining alerts, verifying threats, and working with you to secure and roll back clean data.
Search and destroy cyber threats
Threat hunting capabilities enable search across your backups. Locate and quarantine threats and destroy with defensible deletion prior to recovery.
Beat threats with speed and confidence
Druva Cyber Recovery Runbooks automate recovery plans with scheduled testing, live incident recovery, isolated validation, and audit-ready reporting.
Recover from ransomware fast
Druva’s advanced ransomware cloud data protection and defense-in-depth security are paired with workflow orchestration and recovery automation tools to improve response time, prevent reinfection, and reduce data loss. Plus, Druva’s ransomware SaaS solution delivers 24×7 fully-managed security operations.
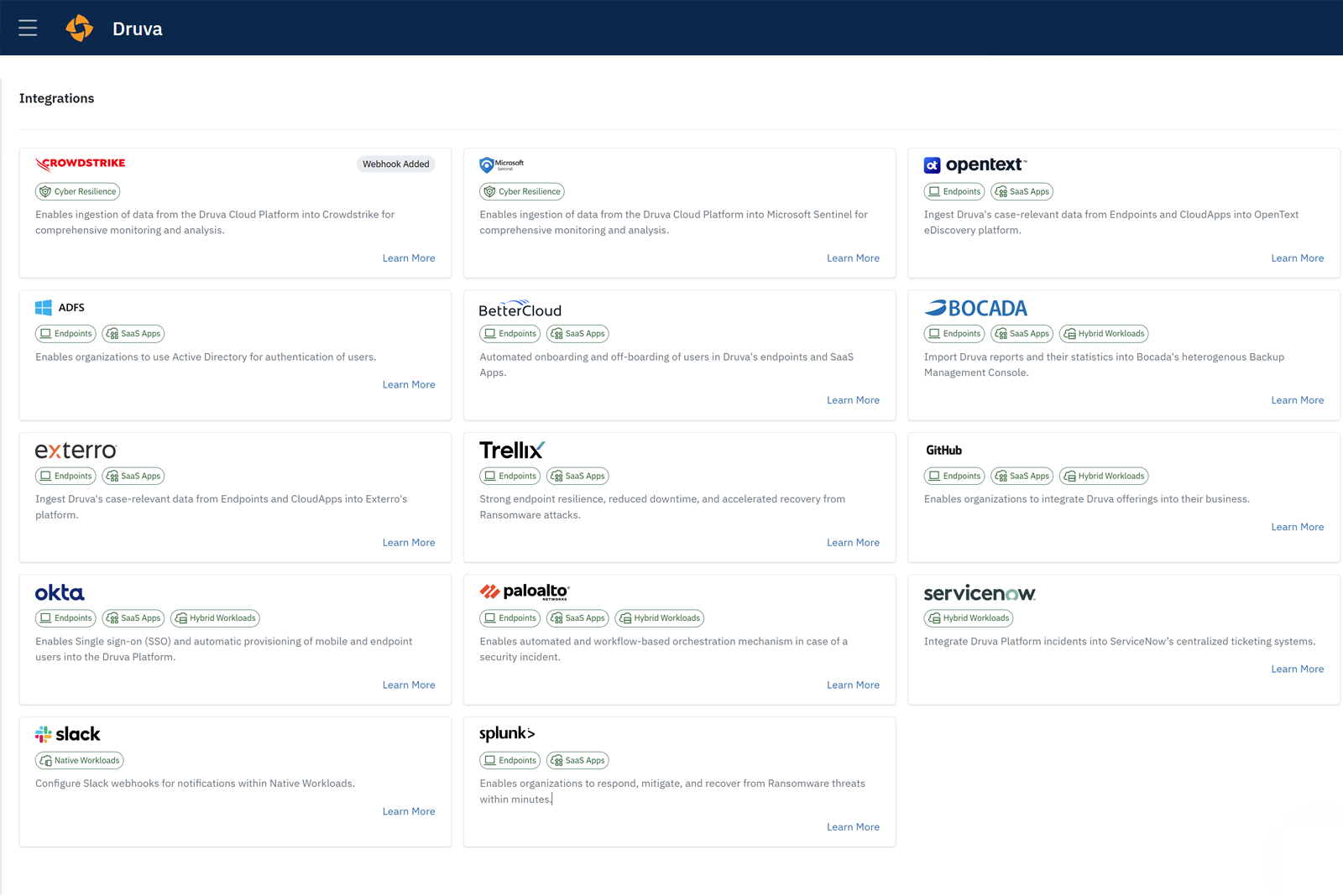
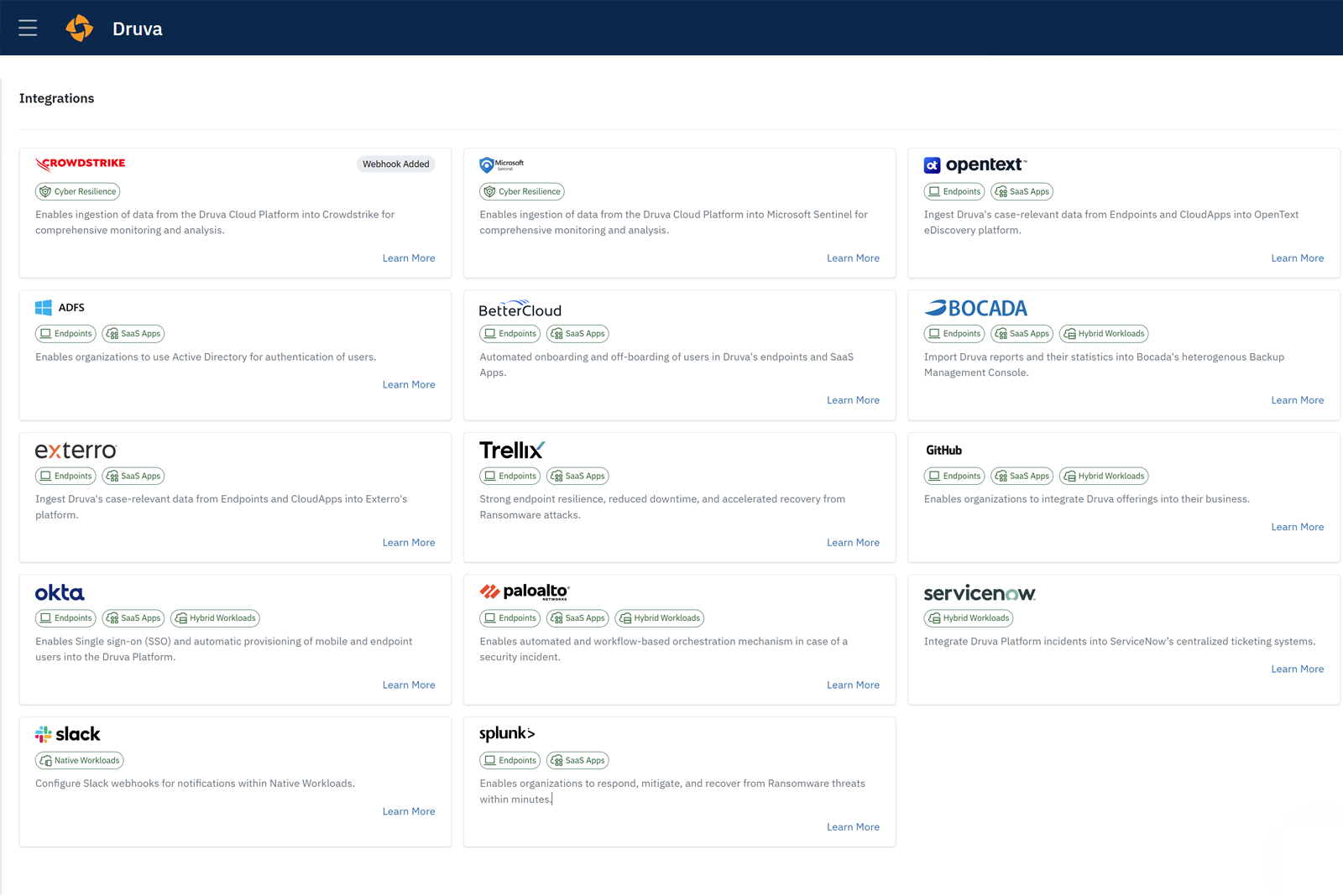
SecOps integrations stream backup telemetry to your SIEM/XDR, enabling faster threat detection and response, to boost cyber resilience.
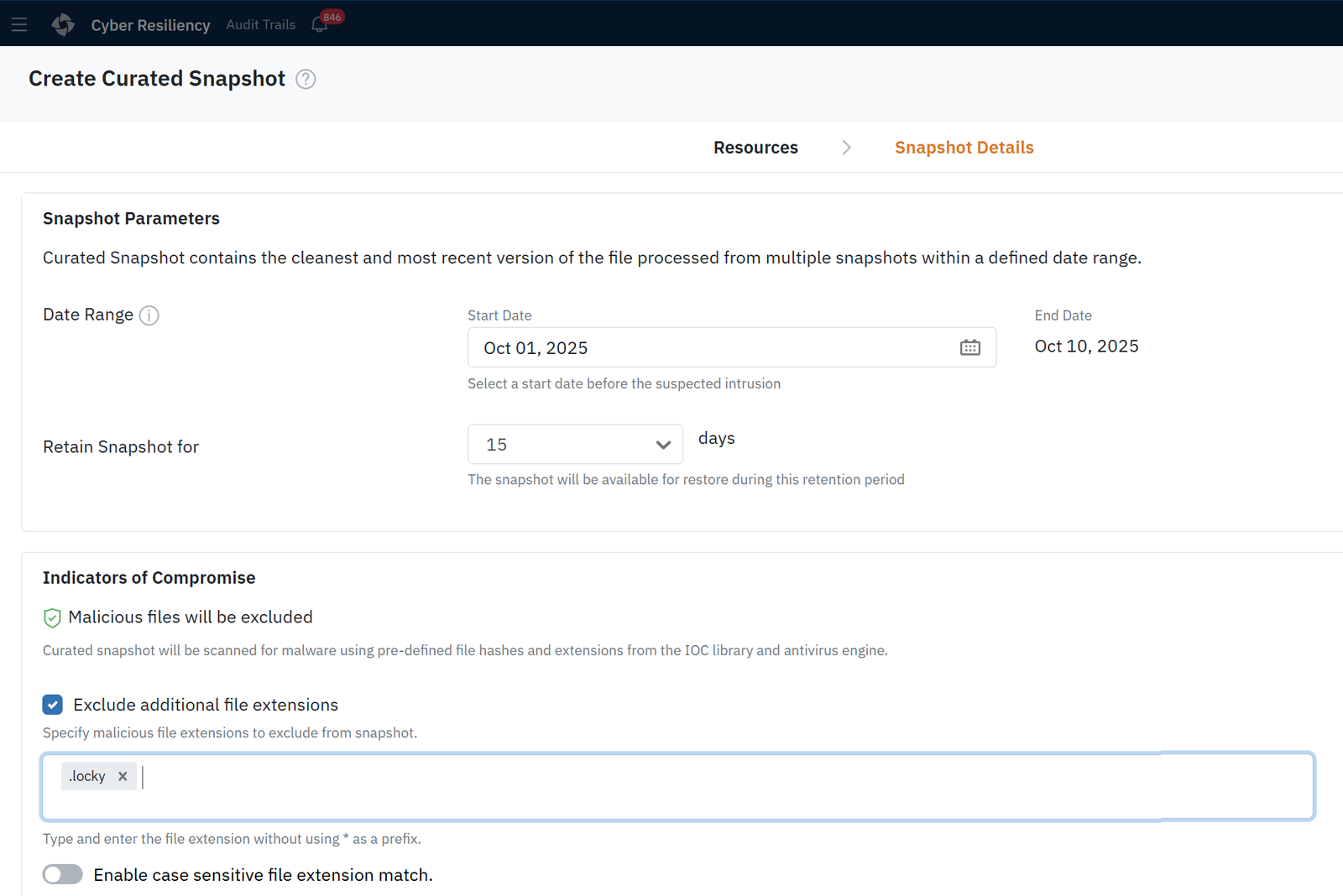
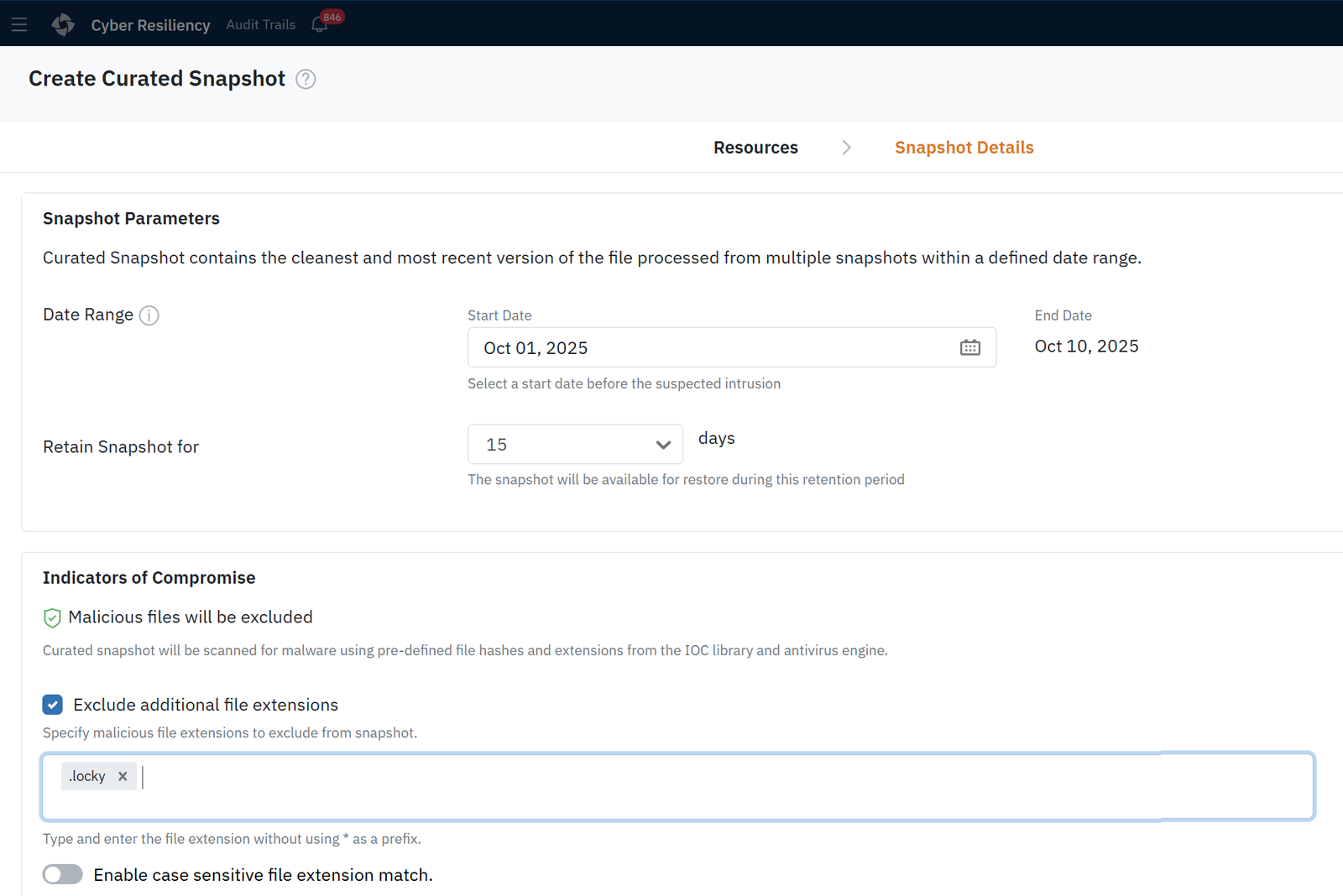
Automatically create a “golden snapshot” with the latest clean file versions from the attack period, ensuring malware-free restoration.