Federated search identifies and locates files, versions, deleted files, departed employee data, storage, and geographical locations via snapshots.
Minimize downstream review and processing cost
Slash costs by up to 40% vs. traditional tools. Process legal holds faster with pre-culled data, minimizing downstream review expenses and boosting efficiency.
Ensure authenticity and minimize data spoliation
Collect and preserve data forensically. Full audit trails and chain of custody prevent spoliation, ensuring compliance and tamper-proof evidence for EDRM.
Preserve in place legal holds
Execute legal holds and searches instantly across data sources. Respond to legal inquiries faster without disrupting users, boosting operational efficiency.
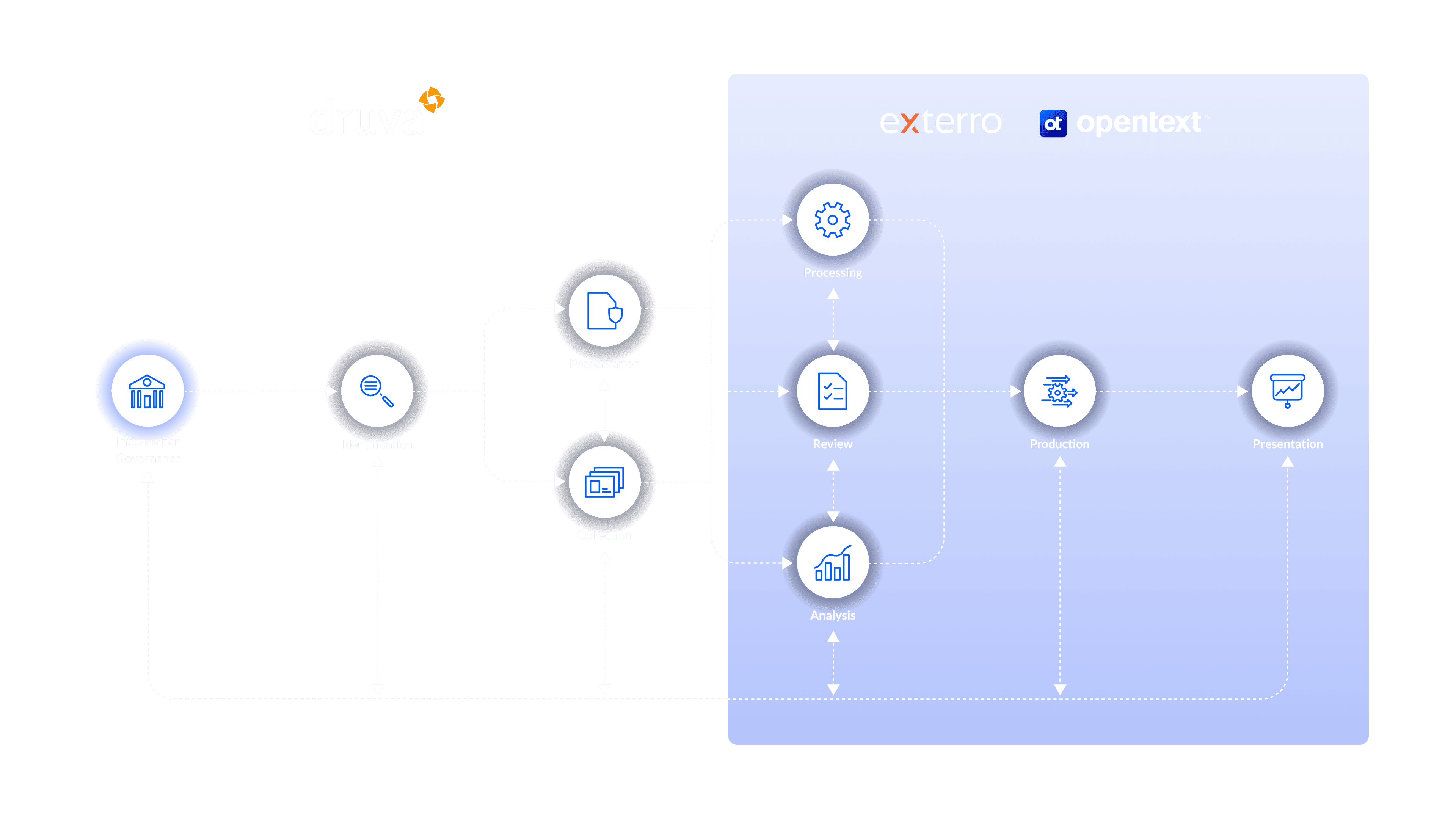
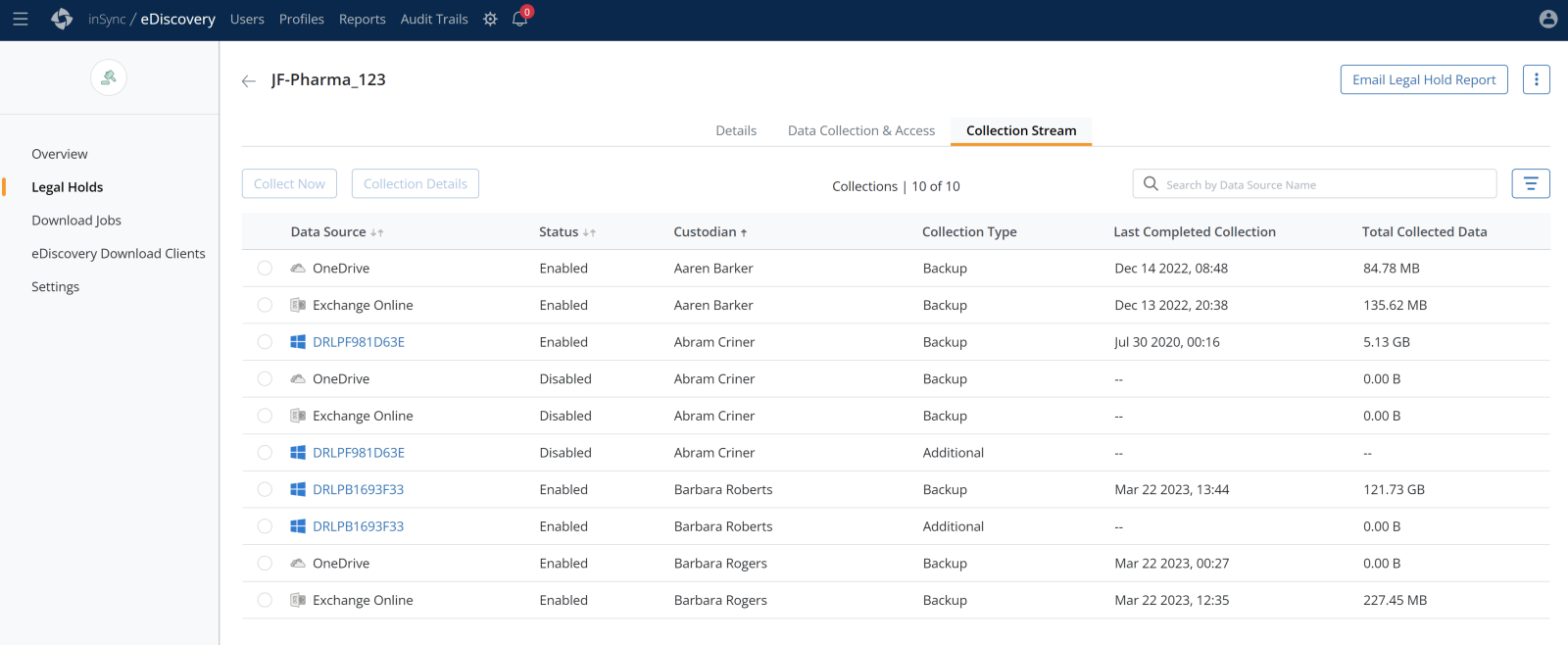
How it works
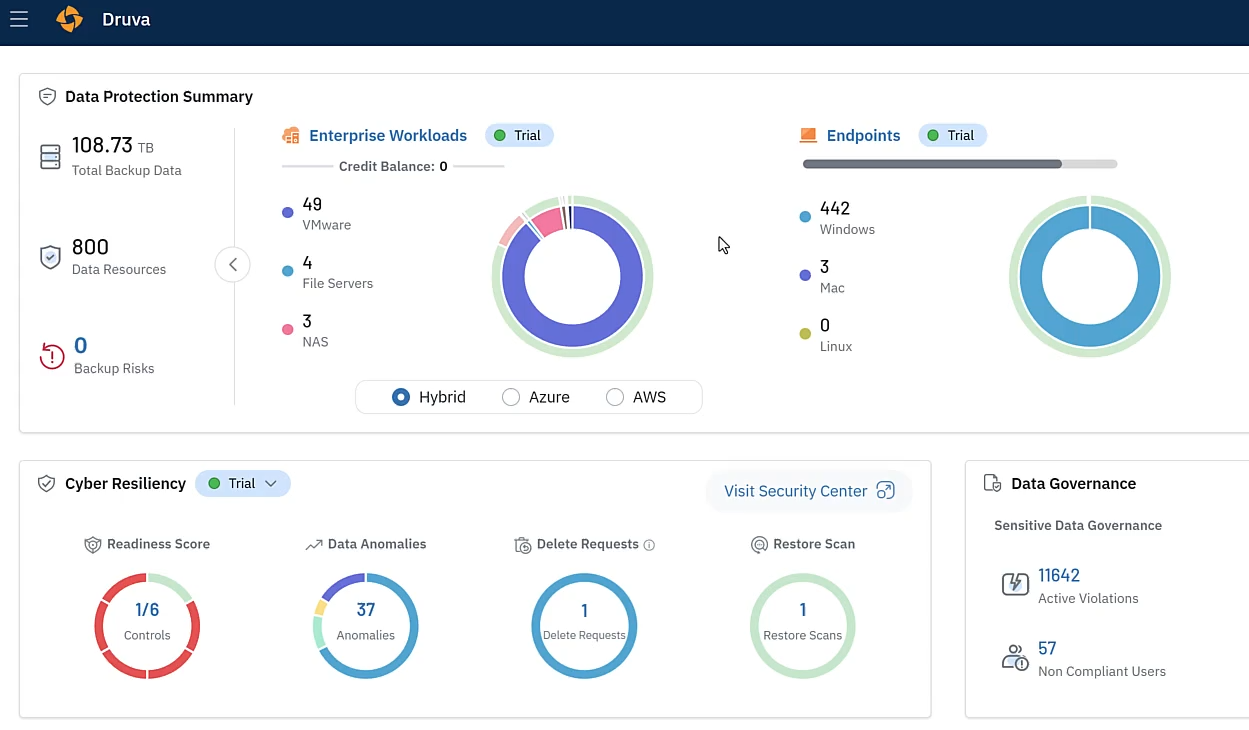
Druva’s solution streamlines eDiscovery data collection and preservation processes.
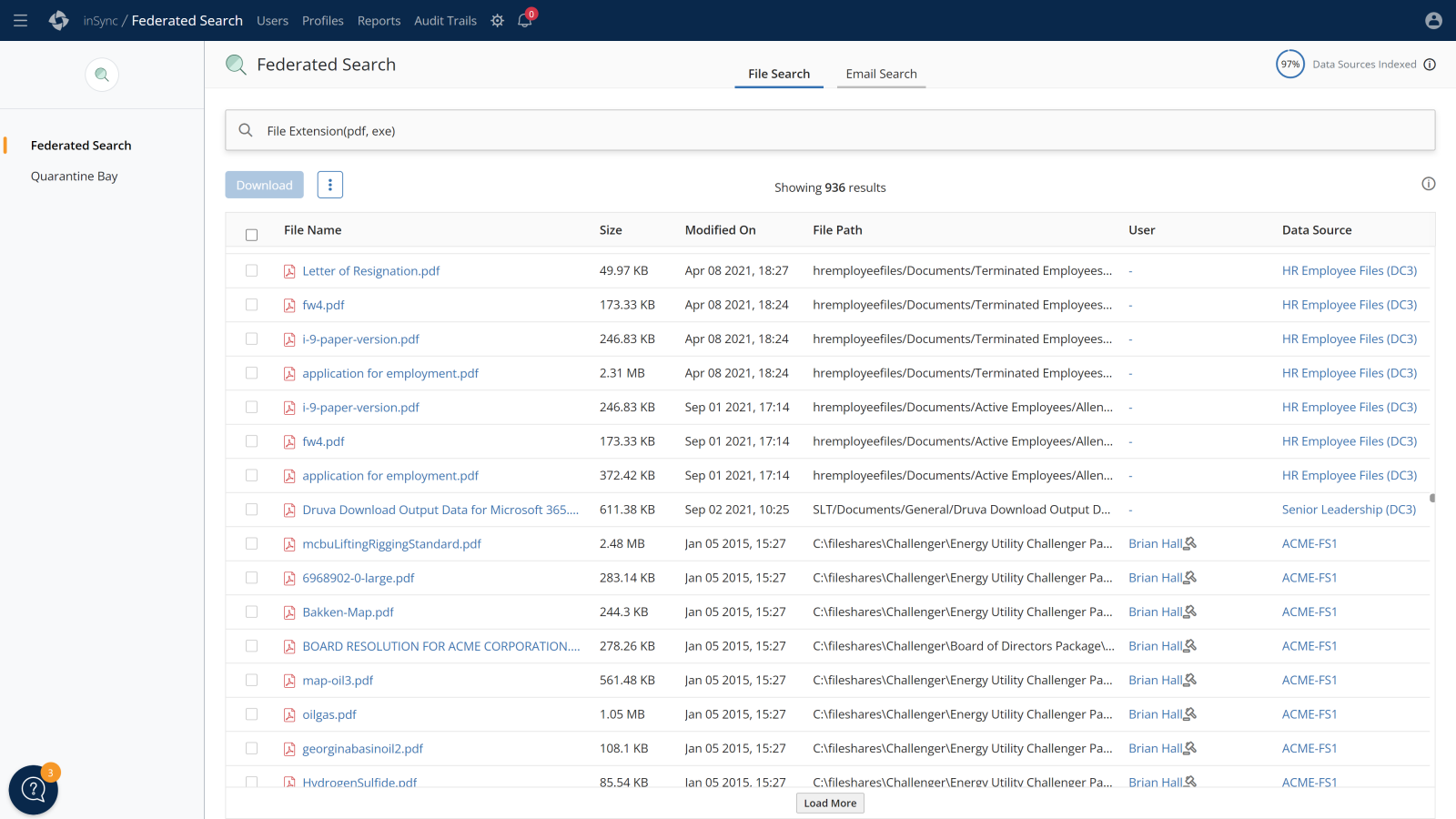
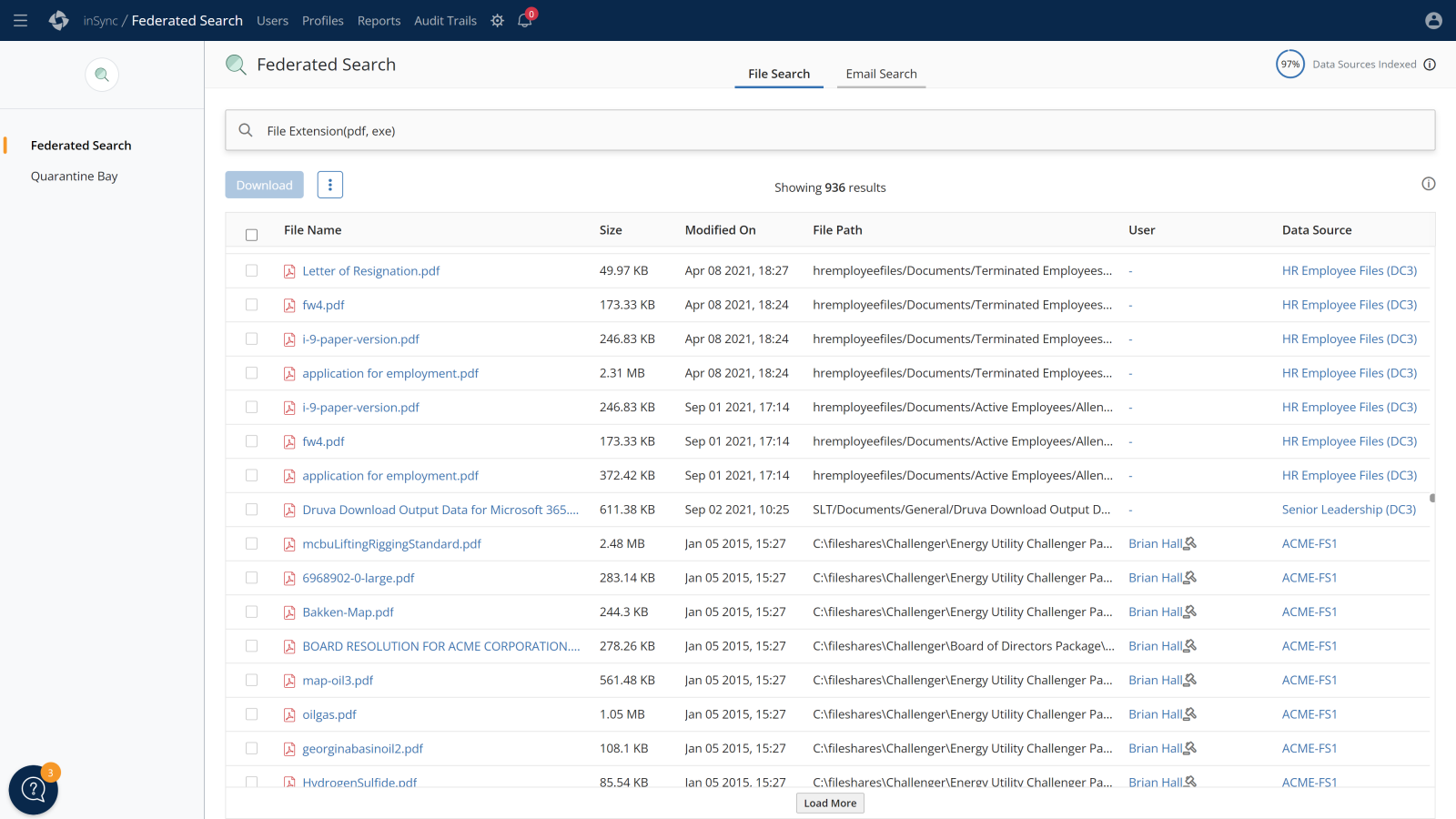
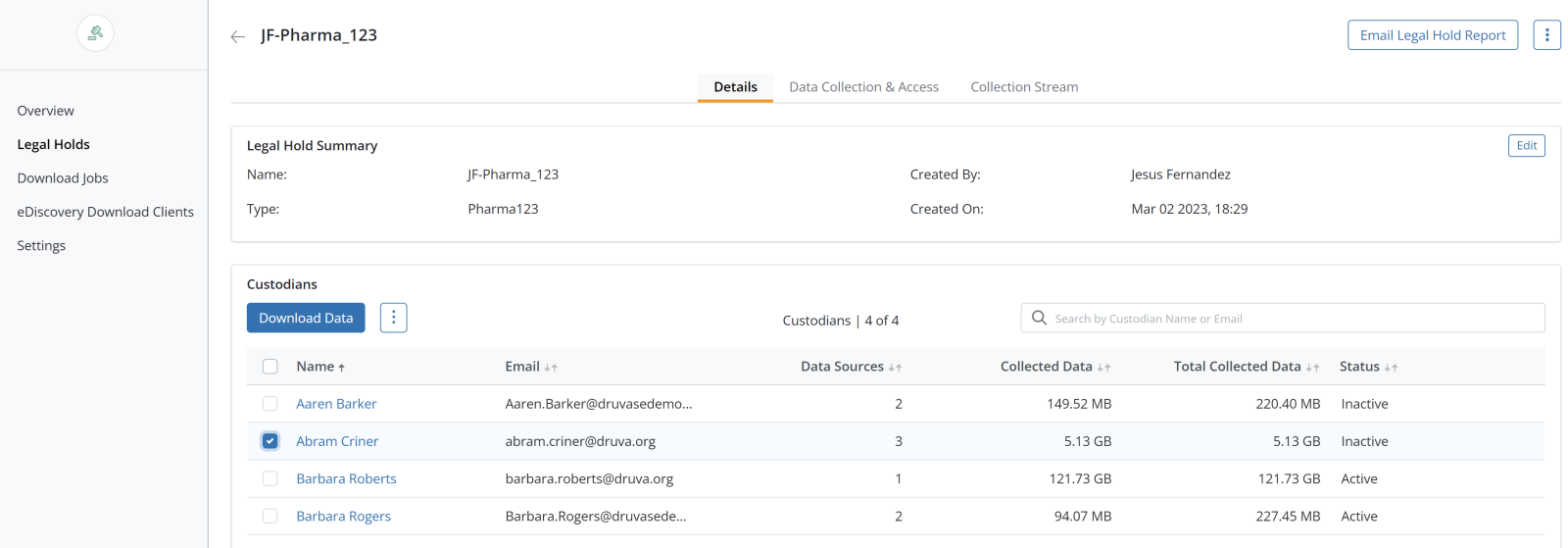
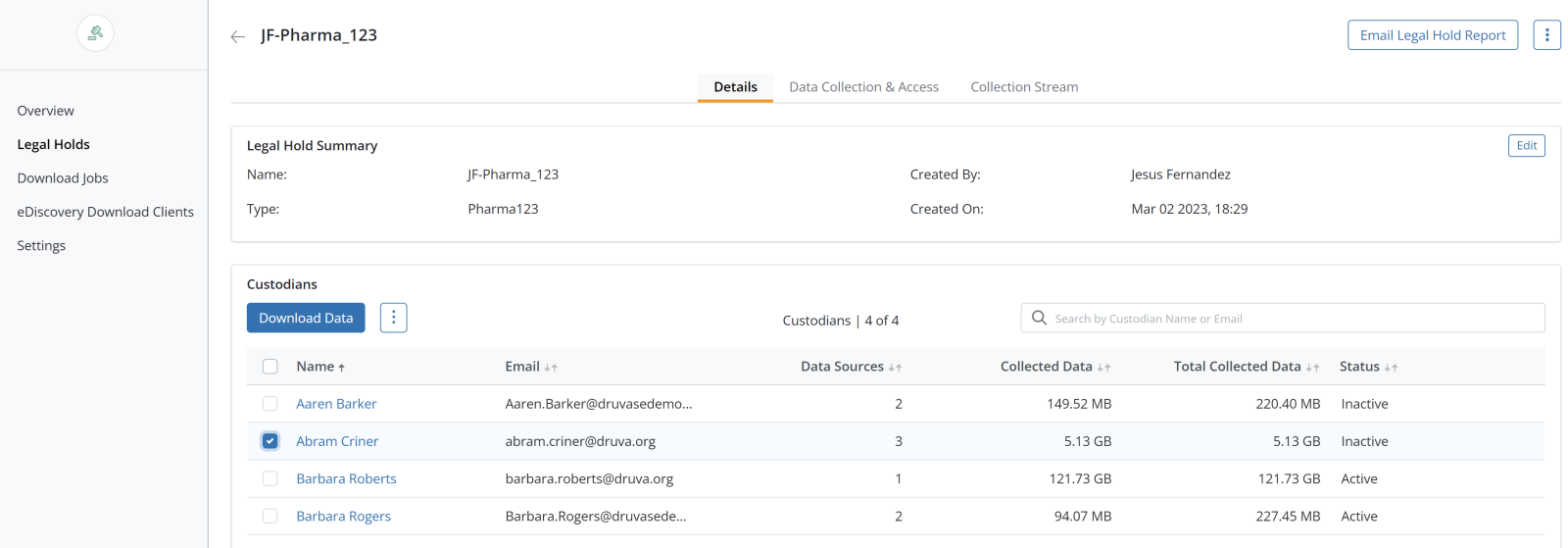
Gain access to review legally held data and expose it for ingestion over the network, accelerating downstream legal processes and review.
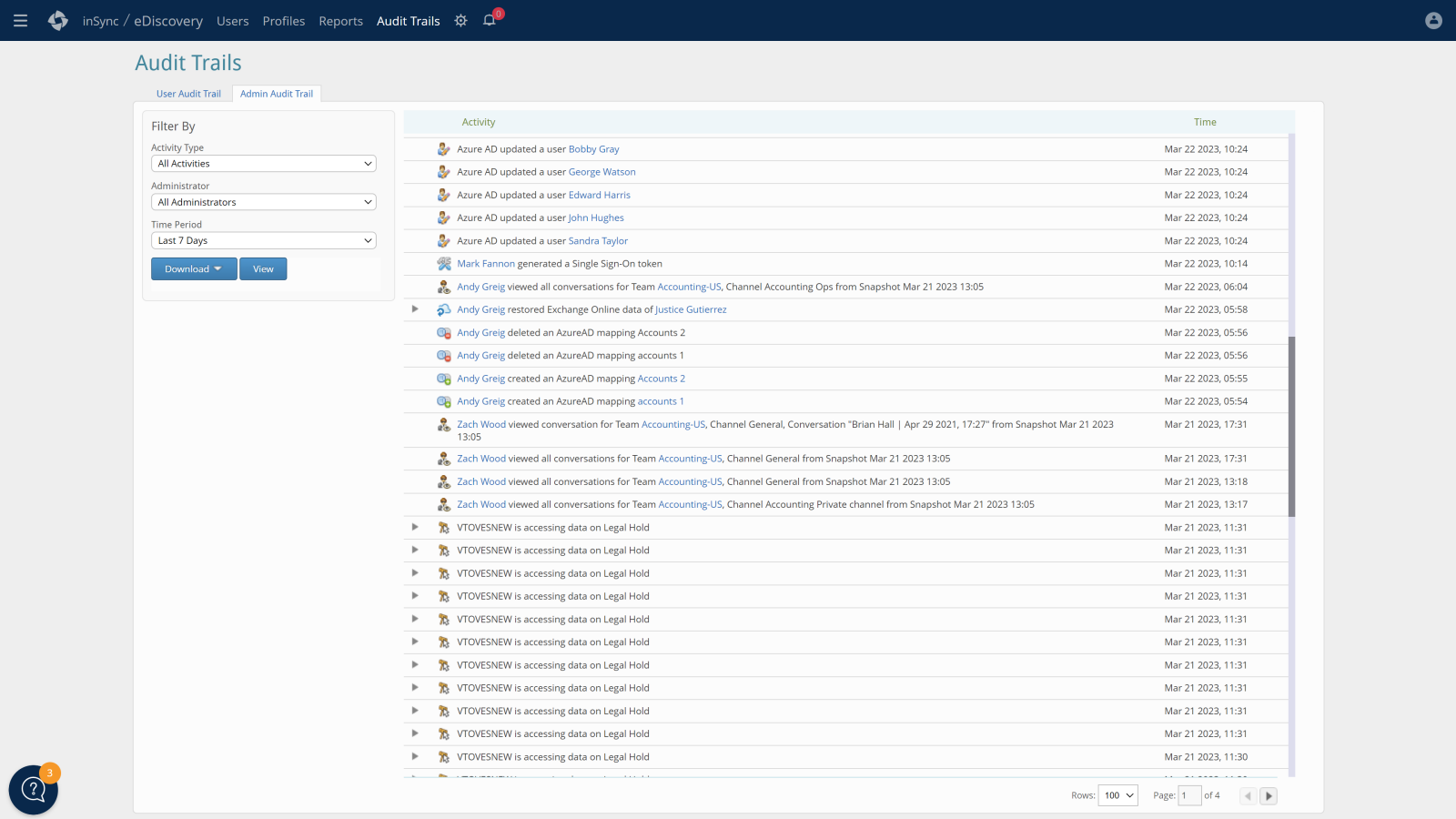
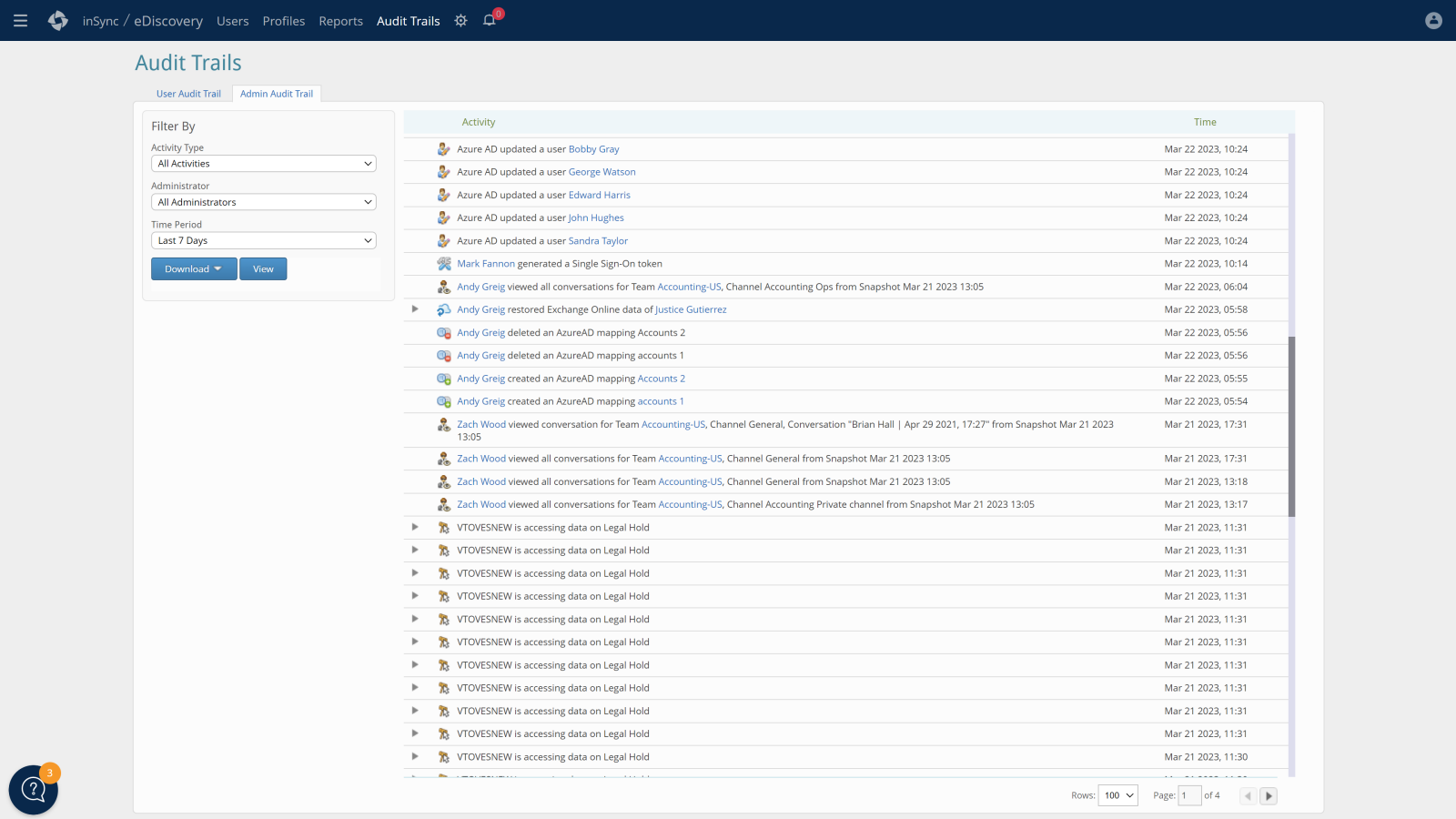
Comprehensive legal hold, tamper-proof audit trails, and secure backups prevent spoliation and preserve defensibility of eDiscovery data.