Druva’s DTC, or direct-to-cloud solution, which we discussed in the previous edition of this blog series, is a game changer in terms of its capabilities, its technological innovation, its novelty, and its utilitarian nature, grounded in elegant design and implementation simplicity. It leverages Oracle serial backup tape (SBT), which is a mainstay of Oracle backup and recovery technology and adds both technical innovation as well as an elegant and simple design. In this blog, we’ll look more closely at how this works and what makes Druva unique.
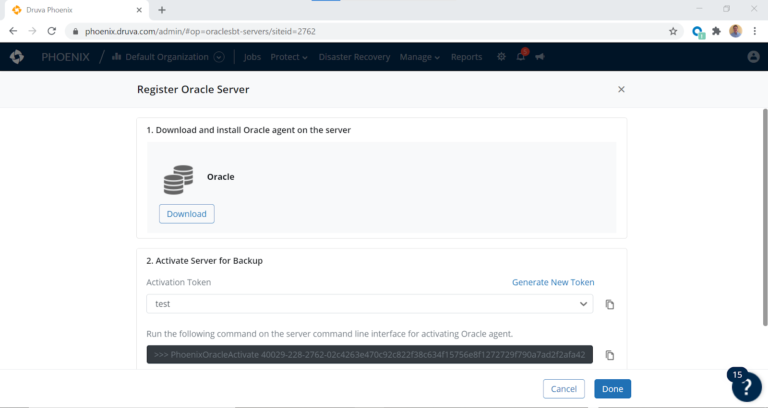
The ease with which Oracle direct-to-cloud can be deployed and leveraged is one of its greatest virtues. The simple download of an rpm file, followed by a quick secure copy (scp) of the file to your Oracle host allows any Oracle and Linux end-user to deploy it on their Oracle relational database hosts as the root super user. This of course necessitates collaboration between the systems administration group and your backup administrator(DBA).
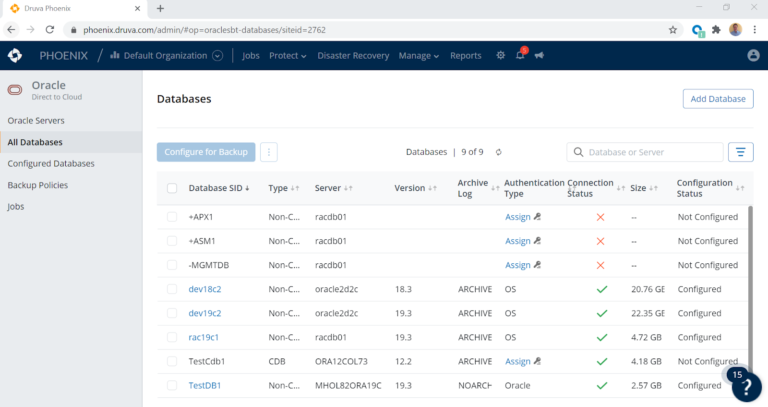
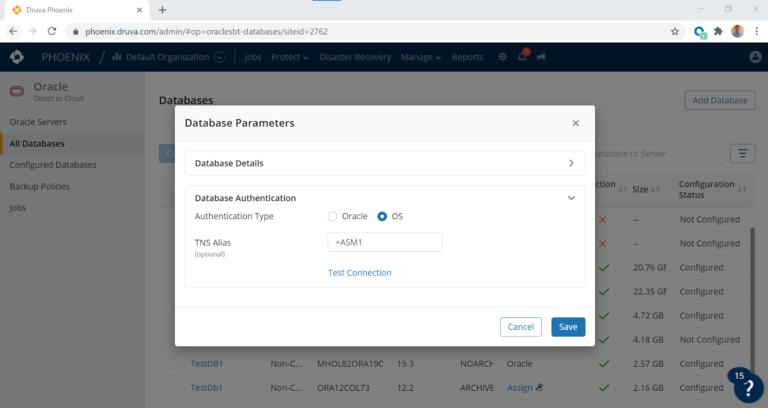
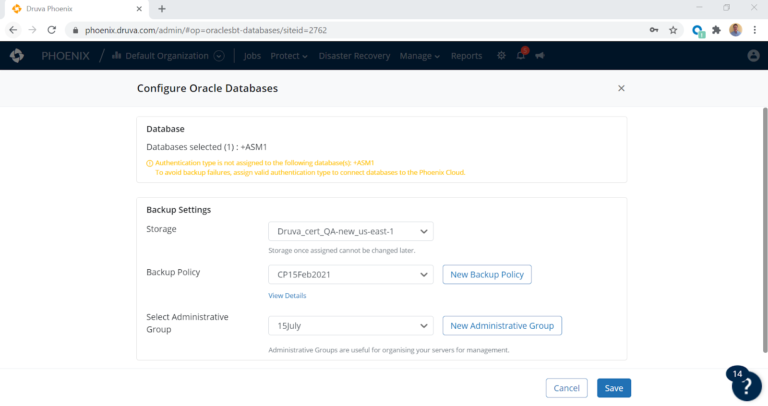
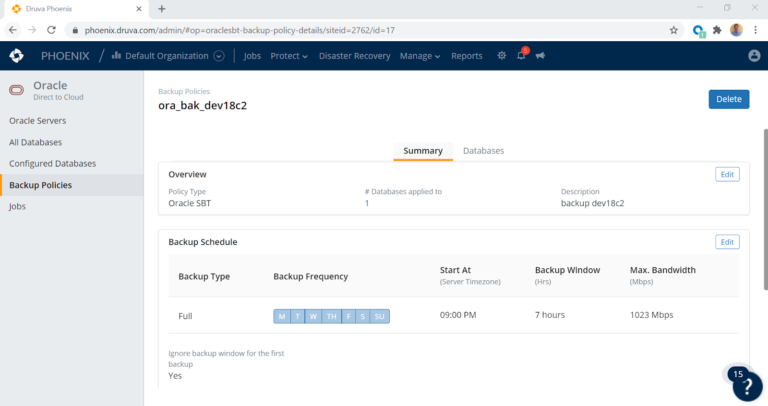
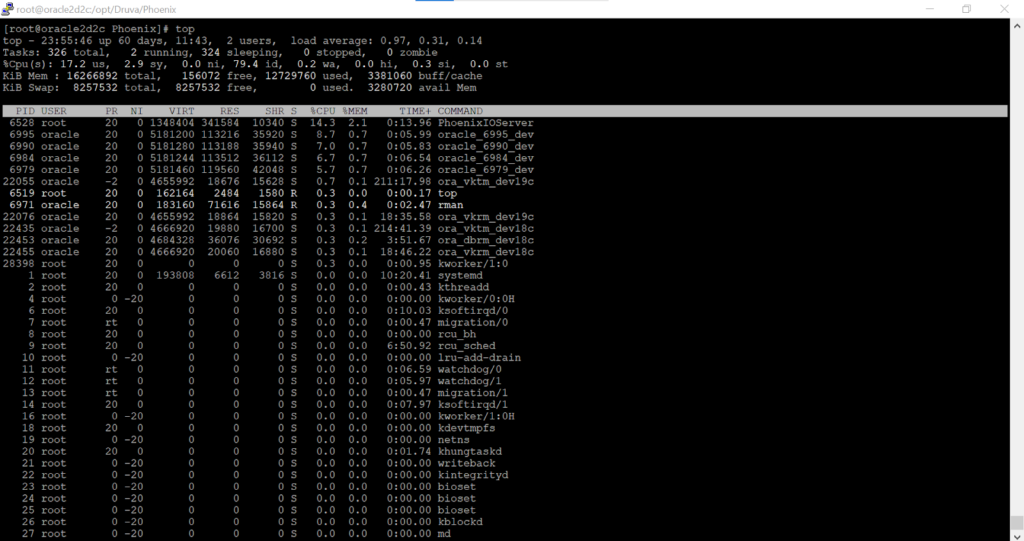
Once the rpm is deployed on the Oracle host, the installation process is very simple — it’s a standard rpm -ivh command to load it into the OS and start the agent. This new technology leverages a very lightweight agent that automatically discovers all Oracle databases on the server and affords the DBA team, or backup administrator, the ability to perform a few simple point and click operations in the UI. These include assigning highly secure and encrypted authentication mechanisms, as well as configuring the attendant database for backup.
Example on a triple node RAC cluster
[root@racdb01 ~]# rpm -ivh druva-phoenix-oracle-client-4.9.3-110108.x86_64.rpm
Preparing… ################################# [100%]
Updating / installing…
1:druva-phoenix-oracle-client-4.9.3################################# [100%]
Starting PhoenixOracle (via systemctl): [ OK ]
The process of starting and stopping the agent is very straightforward. The systemctl binary that all system administrators (SA) are familiar with is leveraged to stop, start, and/or status the agent. The deployment automatically starts the agent, and in order to execute the other commands, the following syntax is required.
Example of a start, stop, and or status command on node one of our RAC cluster
[root@racdb01 ~]# systemctl enable PhoenixOracle
[root@racdb01 ~]# systemctl start PhoenixOracle
[root@racdb01 ~]# systemctl status PhoenixOracle
Druva’s GA release of the code will handle RAC clusters seamlessly by dealing with cluster node failures and performing RMAN backups across cluster nodes. This will load balance any backup activity and stream it in parallel. The EA release officially began in February 2021 and supports RAC as well. The administrator will only deploy the agent to one node only with the EA release. Hence, storage modalities like Oracle’s automatic storage management (ASM) are supported along with filesystem implementations of Oracle, or even single instance ASM deployments. The beauty and elegant simplicity of the agent’s deployment allow the agent to leverage a proprietary C library loaded onto the Oracle host.
Example location of the library deployment and agent on Redhat 7
[root@racdb01 ~]# cat /etc/redhat-release
Red Hat Enterprise Linux Server release 7.7 (Maipo)
[root@racdb01 ~]# cd /opt/Druva/Phoenix
[root@racdb01 Phoenix]# ls -l *
bin:
total 61832
-rwxr-xr-x+ 1 root root 20162360 Feb 25 14:54 PhoenixIOServer
-rwxr-xr-x+ 1 root root 18174296 Feb 25 14:54 PhoenixOracle
-rwxr-xr-x+ 1 root root 9660200 Feb 25 14:54 PhoenixOracleActivate
-rwxr-xr-x+ 1 root root 5455144 Feb 25 14:54 PhoenixOracleSetProxyDetails
-rwxr-xr-x+ 1 root root 9853256 Feb 25 14:54 PhoenixOracleUpgrade
lib:
total 24736
-rwxr-xr-x+ 1 root root 114840 Feb 25 14:54 ca-certificates.crt
-rwxr-xr-x+ 1 root root 25209290 Feb 25 14:54 libphxsbt.so
[root@racdb01 Phoenix]#
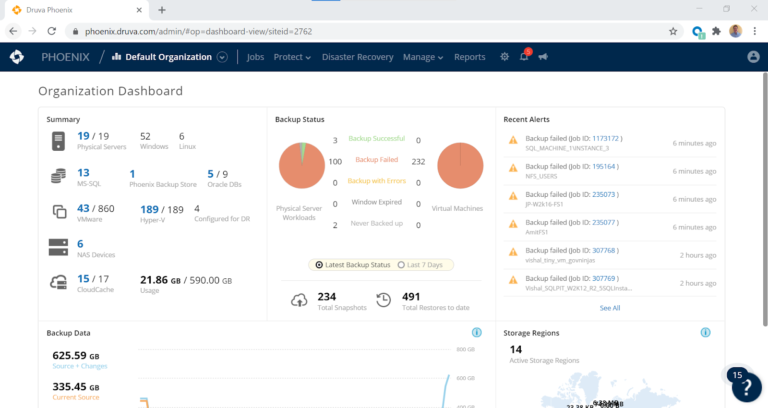
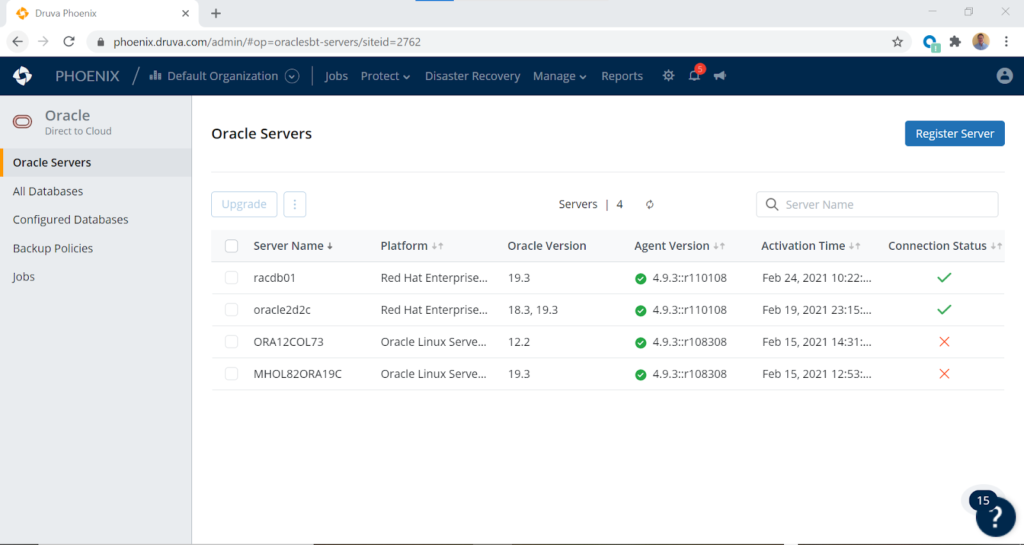
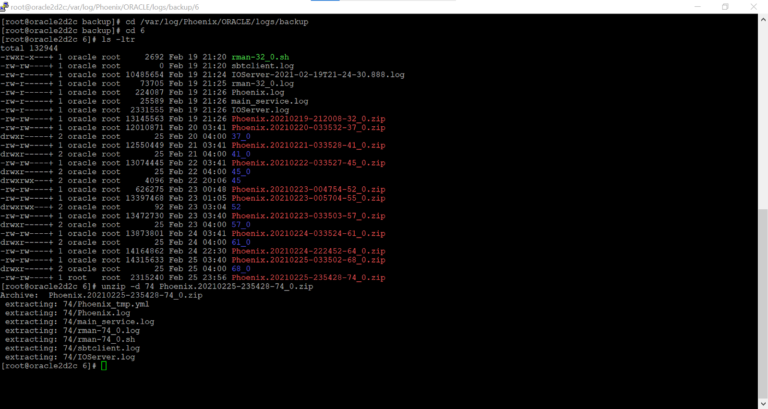
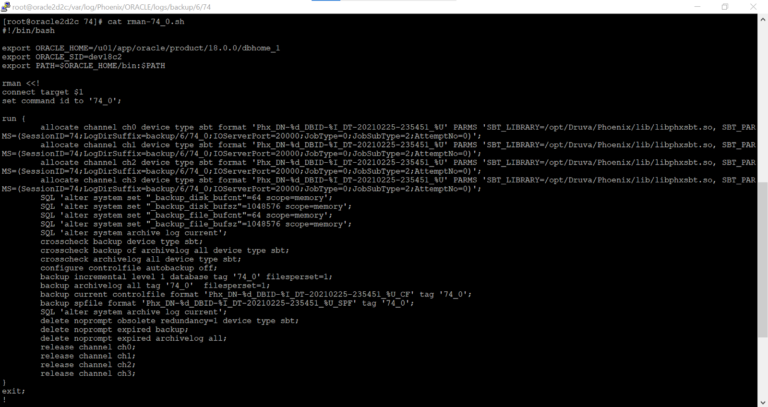
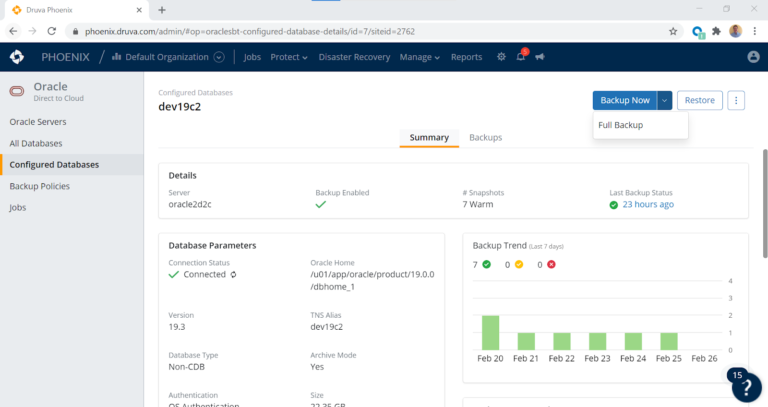
The Druva Phoenix for Oracle SBT tape library handles everything for the DBA and backup administrator. The library performs the deduplication, encryption, and compression of the RMAN-based backup. This greatly simplifies the backup process by removing any need for DBAs to worry about setting hard code RMAN parameters in their database configurations. The agent uses highly-secure certificates such that only the customer has access to their backups in the cloud. The SBT library directly streams Oracle RMAN backups into the Druva cloud and filesystem in the AWS EC2 environment. As such, the backups are not only compressed, encrypted, and deduplicated, they are also protected from any kind of ransomware attack. The backups transmitted to the Druva Cloud are encrypted in flight by the SBT library, and encrypted at rest in the Druva Cloud to ensure complete security and the integrity of your Oracle backup data. Once the SA, DBA, or backup administrator has completed the deployment of the agent and Druva proprietary code to the server, the rest of the work is done exclusively in the UI, including configuration of the databases. The UI makes this process simplistic with a short series of point and click operations.
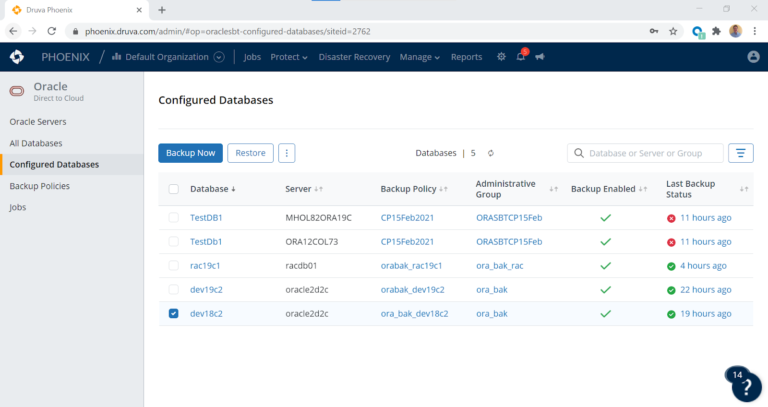
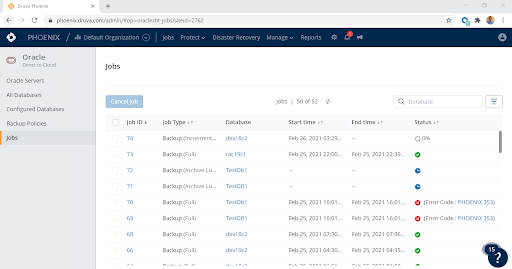
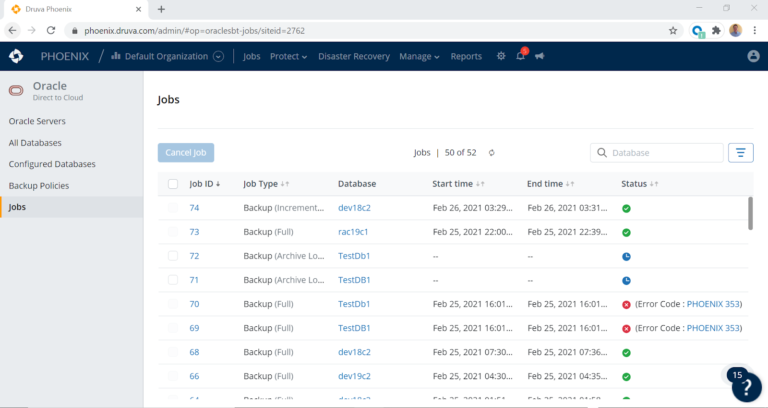
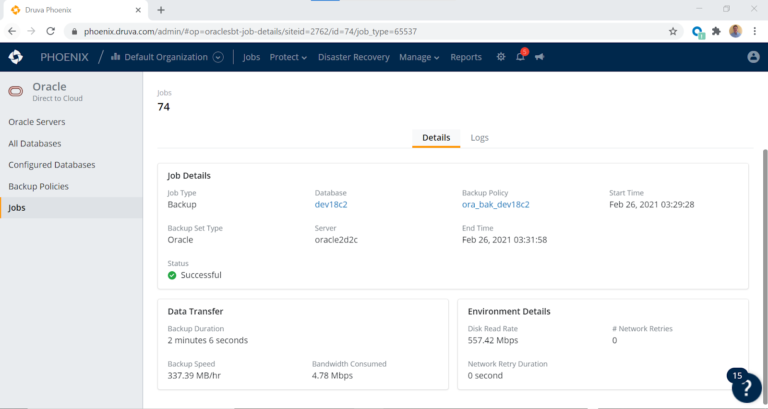
A quick login operation to the Druva console is all that is required to set up the backups.