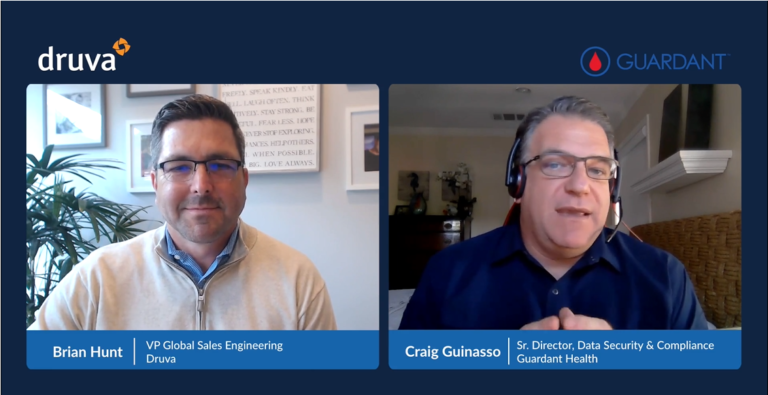
From managing SOC and CERT teams to choosing solutions for their security stack, IT leaders make decisions with colossal consequences. Druva customer Craig Guinasso, Senior Director of Data Security and Compliance at Guardant Health, along with Druva VP Brian Hunt, share top-of-mind ransomware concerns for security leaders: challenges, recovering from an attack, and actionable best practices for cyber resilience.
Major Challenges in Today’s Security Environment
What are you seeing in the cyber resilience landscape?
According to Verizon’s 2021 Data Breach Report, ransomware is targeting healthcare with complex types of extortion. For example, the newest Hive strain of ransomware demands ransom payment for an encryption key and to prevent the public release of confidential information, like medical records. With this double extortion method, threat actors are forcing organizations to find solutions that safeguard their data and quickly recover it.
What are the key challenges that impact IT leaders’ ability to manage data security?
Automation and Orchestration
Craig Guinasso recommends building security strategies like auto manufacturers build safety into cars. Parts of infosec require users to just do the right thing, like putting on their seat belt. Nevertheless, he recognizes that we’re human. Instead of relying on employees to follow security protocol (like connecting to a VPN or reporting phishing emails), organizations should implement safety measures, like airbags and brakes, that protect the systems and data. Implement boundaries around data and identify who should access segments of it, so it can only be used in ways that can’t be compromised.
Integrating Backups
Integrating backups is an added data security challenge for IT leaders. Ideally, you don’t ever want to think about your data backups. If a server or endpoint goes down, you need to quickly restore the data and seamlessly move away from the impacted device with confidence. This, of course, requires the right solution. See why IT leaders have trouble sleeping?