Source: Aberdeen Research for Egress Software
More importantly, let us remember that under the shared responsibility model, Microsoft offers no guaranteed SLAs, and security is dependent on Microsoft’s own analysis and prioritization.
1. Advanced social engineering threats
In late 2020, Microsoft issued a warning about an ongoing phishing campaign targeting its Microsoft 365 users. Microsoft provides anti-phishing and Mailbox Intelligence that focuses on three things – protect, detect, and respond. But then, the first stage is really dependent on reputation lists and policies. At the mail-flow protection stage, all emails must pass through their authentication which includes explicit and anti-spoof frameworks including SPF, DMARC, and DKIM.
However, more than 80 percent of phishing attacks bypass these authentication systems because phishers themselves use DMARC. They can create lookalike domains, or just take over a legitimate customer or supplier email to target your company. This means the phishing email is originating from a legitimate domain and will pass DMARC authentication. Also, remember that implementing DMARC/DKIM/SPF correctly is a big challenge, even for large organizations. Only 20 percent of Fortune 500 companies have implemented DMARC authentication so far. In such a scenario, what happens to your data in case of a breach from advanced social engineering campaigns?
2. Ransomware
In April this year, researchers at Cofense said that attackers were running a spear phishing campaign using a SharePoint document that contained a malicious link to a ransomware code. As the attack slipped through Microsoft’s SEG defenses, it demonstrated that ransomware attacks can easily bypass the detection mechanisms of SEGs. According to Vectra AI research, 56 percent of Microsoft 365 customers sampled exhibited suspicious activity in their environment typical of reconnaissance and data exfiltration malware.² Whether these attacks were specifically targeted at Microsoft 365 or some other system is a moot point. Even if your SQL server gets impacted, there is no guarantee that a lateral movement of the malware will not happen — especially if customers use OneDrive file sync to move data back and forth between their physical infrastructure and the cloud. Once this happens, how do you recover valuable data?
3. Brute force password attacks
To be fair, Microsoft offers multi-factor authentication to protect users and accounts in its cloud environment. Despite this, and also because many organizations do not enable this feature, attacks exploiting user credentials are a widely reported security issue with customers. Brute force and password stuffing attacks are less sophisticated than social engineering attacks such as executive spoofing but they can still be very effective. Microsoft 365 is a popular target among attackers exploiting three key features, one of them being OAuth (the other two are Power Automate and eDiscovery).
4. Insider threats
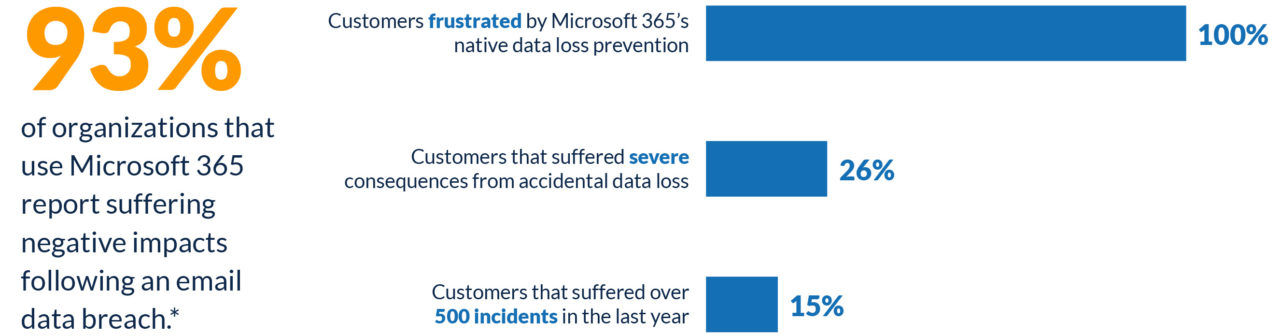
Data loss prevention (DLP) is an add-on feature to most Microsoft 365 licenses with the exception of the most expensive tier, E5. Customers can buy this as part of the Advanced Compliance Center. There are features to identify sensitive information across many locations – Exchange Online, SharePoint Online, OneDrive for Business, and Teams. DLP within Microsoft 365 is mostly based on policies and Microsoft Information Protection (MIP). These can also block the egress of sensitive data from the organization, or encrypt it before it is sent depending on rules the organization establishes. But policy enforcements and the high percentage of false positives can really hinder user experience and productivity. Also, there is no way to identify anomalous behavior (or change in employee behavior) to predict risk. If data gets altered or permanently deleted by disgruntled employees or rogue admins, there is little recourse to recovering it if you don’t have a third-party data backup solution.
5. Accidental data loss
This is probably the most under-reported data loss event across organizations globally. However, this doesn’t mean the risk does not exist. According to the Verizon Data Breach Investigations Report, 85 percent of data breaches involve a human element.³ If an employee accidentally deletes critical data or even an entire SharePoint site, how do you ensure data recovery? Outlook allows an end user to recover individual mails for a theoretically unlimited amount of time (depending on admin thresholds), and 14 days from the recoverable items folder — or you can put a litigation hold on sensitive files to prevent deletion. But for bulk deletions such as SharePoint sites, the recovery has to be admin-driven, which is a very complex process.
Key takeaways
To sum up, there are really only two ways to ensure your data is safe on Microsoft 365. The first is to settle for native data protection features and embrace complexity, suffer unlimited data sprawl (never delete anything, keep multiple versions of data), and face unpredictable costs. Or invest in a simple third-party data backup solution that not only consolidates management across multiple workloads and cloud applications, but also ensures speed, performance, low and predictable costs, and peace of mind.
Now that we have defined the problem, let us focus on how to solve this, with:
- Multi-layered data security that protects your data in motion and at rest
- Immutable cloud backup to ensure that data is not tampered with or altered
- Advanced automation to reduce the risks with manual data backup configurations
- A single pane of glass for centralized visibility and management of all your data across multiple applications, users, and locations
- Flexible and granular recovery
- A simple, secure platform that future-proofs data security
Download “The Gorilla Guide to Comprehensive Microsoft 365 Backup” by ActualTechMedia, to learn more, and read part two in this blog series, “How to fill in the gaps for Microsoft 365 data protection,” to further explore the complexities of cloud data protection for Microsoft 365.
¹Egress, “Outbound email: Microsoft 365’s security blind spot,” May 11, 2021.
²Vectra, “What We Saw in 90 days from 4 Million Microsoft Office 365 Accounts,” October 13, 2020.
³Verizon, “Verizon 2021 Data Breach Investigations Report,” May 13, 2021.